

Slide 1
Slide 2
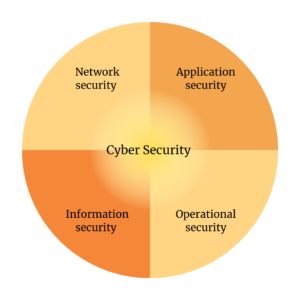
Cyber Security
Cybersecurity refers to the methods used to safeguard electronic devices, networks, and data from malicious attacks, whether it be in business or mobile computing. It is also known as electronic information security or information technology security, and can be categorized in a few ways.
Insights
“Protecting Against Digital Threats: The Importance of Cybersecurity”

Network Security

Security measures for protecting a computer network from intruders, including both wired and wireless (Wi-Fi) connections.
Application Security
Processes that help protect applications operating on-premises and in the cloud. Security should be built into applications at the design stage, with considerations for how data is handled, user authentication, etc.
Information Security
The General Data Protection Regulation (GDPR) and other similar measures are implemented to ensure the security of your most confidential data, guarding it against unauthorized access, exposure, or theft.
Operational Security
The term encompasses the procedures and choices involved in managing and safeguarding data assets. This encompasses factors such as user permissions for accessing a network, as well as the protocols for storing and sharing data.
Storage security
The data resilience provided is exceptionally reliable, featuring multiple safeguards such as encryption, as well as isolated and immutable data copies. These copies are stored within the same pool, enabling swift restoration to aid in recovery and reduce the impact of any potential cyber attacks.
Mobile security
With app security, container app security, and secure mobile mail, you can effectively manage and safeguard your mobile workforce.
Our Offerings
“Fortifying Your Defenses: Our Comprehensive Cyber Security Solutions”
Service Offerings
- Network Security
- Application Security
- Information Security
- Operational Security
- Storage security
- Mobile security
Request for services
Discover how we can assist your organization in navigating its next phase. Please inform us of your specific areas of interest so that we can provide you with more personalized assistance.
